When a pair of homemade bombs exploded in the midst of a crowd of onlookers at finish line of the Boston Marathon four years ago, the attack exposed gaps in U.S. national security.
The threat from terrorists has since evolved in some ways while becoming less complex in others. So the strategy of law enforcement community to prevent the next attack on U.S. soil has evolved in a similar way.
While low-tech CCTV cameras helped law enforcement identify Tamerlan and Dzhokhar Tsarnaev, it failed to stop them in the first place. “Part of the problem is that when everyone is surveilled, then authorities lose their focus,” said Carol Rose, executive director of the ACLU in Boston, told The Verge.
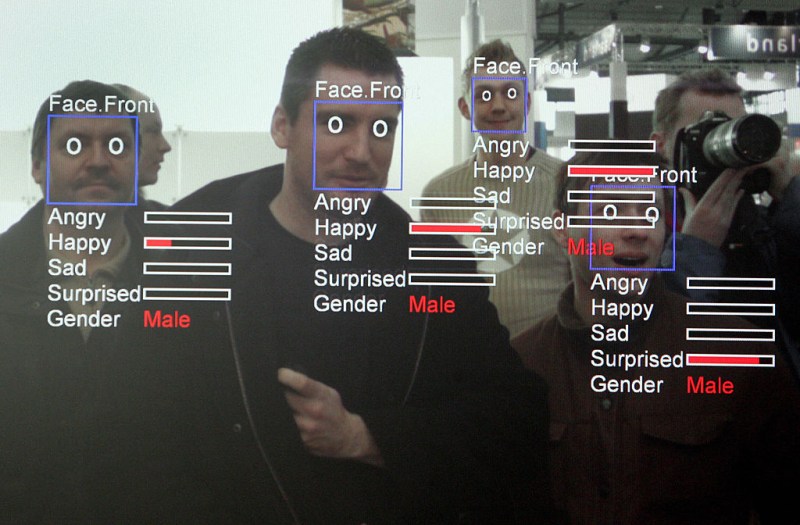
To help minimize that problem, law enforcement officials have turned to artificial intelligence. Facial and object recognition software can help cops and other security officials identify someone in the course of the investigation, but pinpointing an attacker before they can use the weapon is more difficult.
Just months after the bombings, the Department of Homeland Security tested facial recognition software on crowds at a venue in Washington State, but scanning large groups of people requires high-performance computers. Even then, would-be attackers might slip under the radar unless the individual is known to authorities.
That’s where DIVA, or Deep Intermodal Video Analytics, enters the picture. The program proposed by the U.S. intelligence community can analyze live video to spot separate warning signs and connect them to identify suspicious behavior patterns in real-time, Defense One reports. Current privacy laws, however, could prevent the system from being installed.
“We’ve always known the limits of what we could do in a free society, and this week we saw those limits in all their horror,” said Rep. Adam B. Schiff, a member of the House Intelligence committee, to The Washington Post in the days after the attack. Despite the extraordinary build-up of security measures to make Americans safe after 9/11, the crowds assembled near the finish line of the Boston Marathon were the type of target for terrorism that policymakers had long feared.
Routine security measures like metal detectors are often criticized for the lines they cause, and rightfully so, since those queues can then become targets. ISIS suicide bombers, for example, targeted security lines outside the Istanbul airport in 2016. However, some detectors, like the Evolv Edge, are faster and more capable than traditional ones. The high-tech gate can scan ten people per minute for metal and non-metal objects, using a range of sensors and AI, according to TechCrunch.
For outdoor events, like marathons or baseball games, security officials now have to worry about drones. ISIS has been using off-the-shelf drones to attack Iraqi forces on the battlefield, causing law enforcement to fear similar style attacks closer to home.
For the last three years, DroneShield touted in a statement that its radar systems have been deployed at the Boston Marathon to identify unauthorized drones and disable them if need be.
This year, though, the skies over Boston will be buzzing on Patriot’s Day. The city will be using the high-tech solution to watch over one million spectators along the race route. According to the Boston Herald, the drones provided by CyPhy Works (above) have long-distance zoom lenses and infrared cameras to spot potential danger from the air.
Unfortunately, though, the hardest attacks to stop are the easiest to plot. “The attack in London brings to the forefront how rudimentary the planning process may be to be able to conduct a successful attack and cause devastating results,” FBI Special Agent-in-Charge Hank Shaw told the Boston Herald of the March 22 terror attack near Britain’s Parliament Building.
To prevent low-tech attacks like the one’s seen in Stockholm, London, Berlin, and Nice, Boston Police aren’t using AI or robots. Instead, they’ll be using good old fashioned trucks to guard crowds at the finish line and other areas from cars ramming into crowds.
Sometimes, no matter how much technology advances, a simple solution works best.
—RealClearLife
This article was featured in the InsideHook newsletter. Sign up now.