As highlighted by the recent WikiLeaks dump, the same technology that makes life more convenient raises important questions about privacy and security in the 21st century.
“The Internet of Things,” or IoT, is industry speak for the ever-growing collection of objects that use the web to enhance the services they provide. This includes a wide range of technology, from smart home appliances and security systems to phones and self-driving cars
While IoT devices allow leaps in convenience, like ordering a pizza without lifting a finger, there is an increased potential for the violation of privacy and vulnerability to cyber attacks.
The “Weeping Angel” technique, which basically allows hackers to turn a Samsung smart TV into a microphone, is one of the more headline-grabbing nuggets from the cache of CIA files shared by WikiLeaks. Alarming reports missed the fact that the tool is installed from a USB drive, not remotely. So, somebody is required to physically be in the same room as that TV, in order to modify it for spying. “At that point, you probably have bigger things to worry about,” said Dave Bittner, host of the CyberWire Podcast, which shares daily updates on the latest in cyber security.
Nevertheless, Bittner thinks high-profile cautionary tales like those sparked by Vault 7 can be valuable because they help start a public conversation about privacy and security in a world saturated with Internet-connected devices.

On the whole, the more nefarious threat to privacy comes from criminals, not Big Brother. Given this, issues of privacy are overshadowed by issues of security. Baby monitors and security cameras were some of the earliest IoT devices to become popular, and as a result was among the first to be targeted. As reported by ArsTechnica in 2015, vulnerabilities in baby monitors could be used to watch live feeds, steal videos stored online, and change security settings to authorize remote access to any number of people.
Those vulnerabilities have since been patched, but more devices on the market only mean more ways for criminals to exploit them. Shodan, a Google-like search engine for IoT devices, has a section for vulnerable webcams that lets users watch feeds from all over the world, CNBC reports.
The security of IoT devices has become a greater priority for the tech industry, but there’s still room for improvement. Bittner says part of the reason IoT devices remain an attractive target for cyber criminals is because they can be infected with malware and continue to work just fine. That is, until a cyber criminal chooses to use those devices to create a botnet for a DDoS attack, which paralyzes a network with a wave of traffic from webcams and DVRs.
Netflix, for example, was disrupted along with much of the Internet during last October’s DDoS attack, which used the largest botnet in history according to The Guardian. Those types of cyber attacks, though, are of little concern to the average user of smart home devices given the damage to them is limited to a short-term inconvenience. However, Bittner points out the potential for IoT devices, particularly smart home technology, to affect individuals more directly.
Another reason why these Internet-connected appliances are targeted is because they increase the “attack surface,” Bittner says. That’s a term used by cyber security professionals describing the number of ways an attacker can gain access to a system and get data out. What starts with a hacked webcam can quickly become something more dangerous than a digital peeping Tom. “They can move laterally within your network to access other devices,” Bittner says. He describes a nightmarish hypothetical scenario where a networked thermostat, like the popular Nest, is compromised just before an impending blizzard and criminals threaten to turn off the heat if a ransom isn’t paid. “That’s a scenario that could potentially have life or death consequences,” Bittner said. A situation like that is possible today—albeit unlikely to happen to the average person. But as devices in the IoT family grow, so does the attack surface.
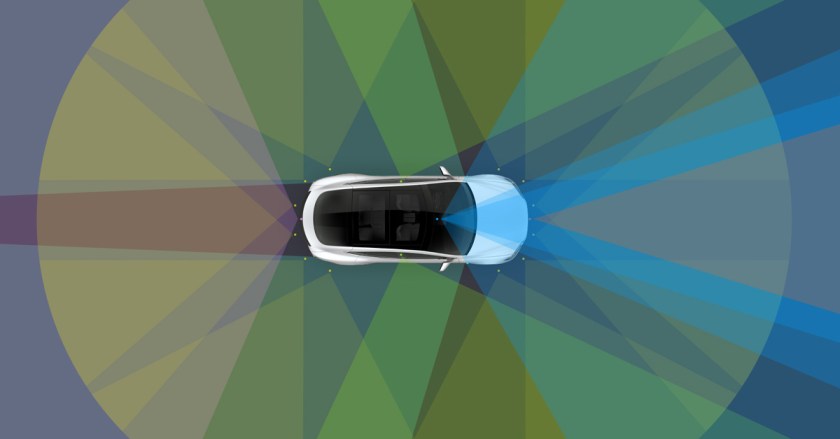
Looking forward, Bittner thinks autonomous vehicles will present new challenges in privacy and security. He thinks cars and trucks could also be held for ransom. Depending on the cargo, trucks could be especially attractive to cyber criminals because can be they can divert them off their programmed route and the steal the trailer’s contents, Bittner hypothesizes. Hacking into the control systems of self-driving cars is already well documented.
According to Business Insider, Tesla is the first fully-autonomous vehicle expected to hit the road and it’ll be ready by 2018, but regulations mean it will be delayed to either 2020 or 2021. That means, industry professionals have about three years to work out these potential vulnerabilities.
And hackers won’t be idle during that time, either.
This article was featured in the InsideHook newsletter. Sign up now.